Executive Synthesis: The Strategic Pivot to Digital Sovereignity
The rapid centralization of fundamental internet services, particularly email and file storage, has transformed convenience into a critical vulnerability. As entities increasingly rely on dominant technology platforms, the imperatives for digital sovereignty—the active reclamation of control over one's own data infrastructure—have moved from ideological preference to strategic operational necessity. Self-hosting, beginning with the foundational component of email, offers a definitive path toward mitigating the profound systemic risks inherent in centralized reliance.
The Economic and Ethical Costs of Centralization
Digital sovereignty, in a professional context, is defined not merely by privacy but by operational resilience, regulatory compliance, and risk avoidance. Relying on "free" services incurs the implicit cost of ceding ultimate control over critical communications and data assets. These third-party corporations retain the unilateral authority to enforce policy changes, apply arbitrary account suspensions, or experience service outages outside the user’s control.
When mission-critical infrastructure, such as email or primary file synchronization, is hosted entirely on a centralized provider, a service disruption or account suspension event results in immediate, catastrophic operational failure—the inability to receive contracts, communicate with clients, or access essential archival files. Self-hosting actively eliminates this single point of failure represented by centralized account governance. By deploying and maintaining local infrastructure, the user guarantees complete data ownership and reinforces business resilience, transforming the deployment into a mandatory operational risk mitigation strategy.
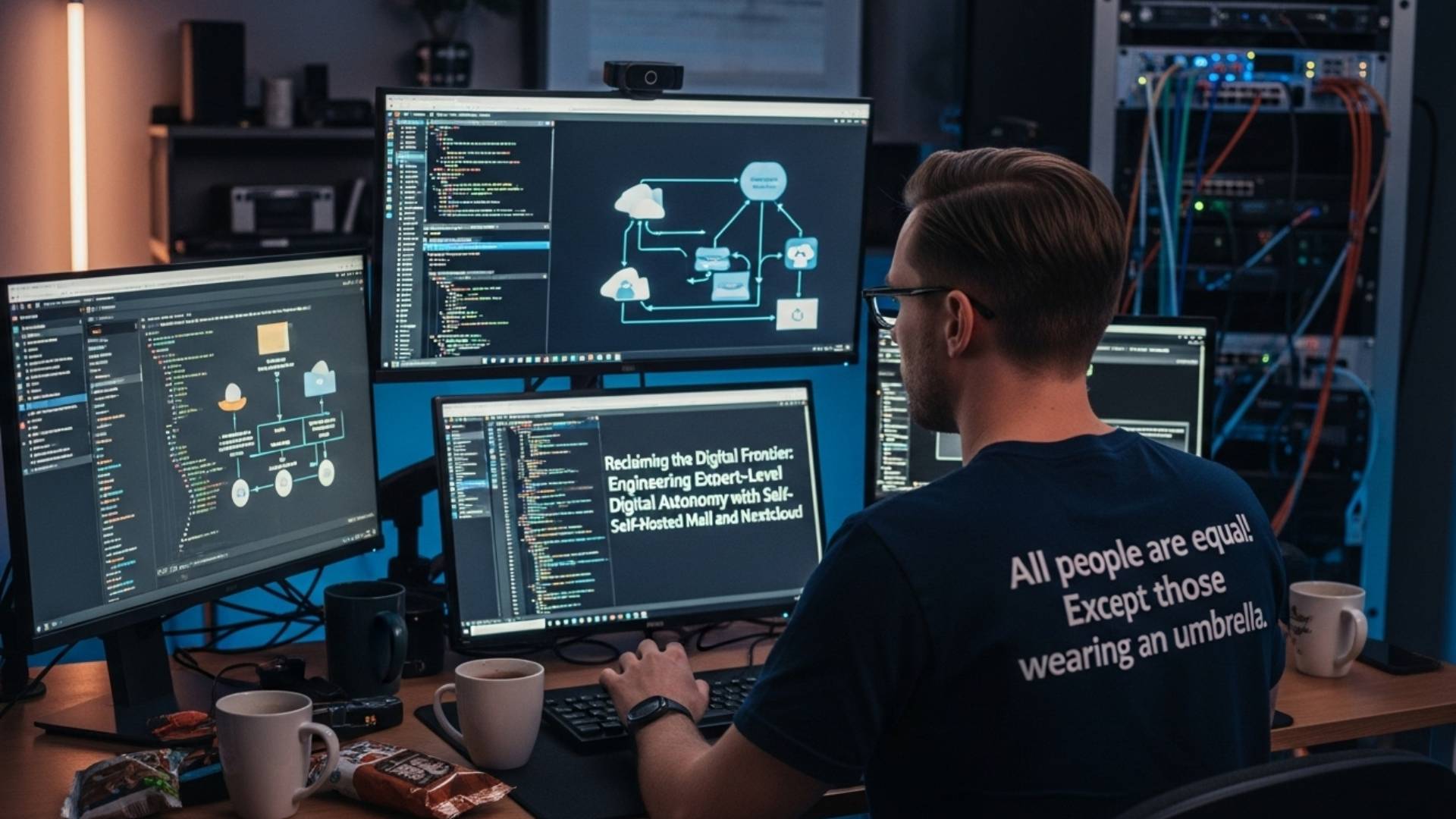
Architecture of Autonomy: Turn-Key vs. Modular Approaches
The decision to self-host requires selecting a deployment architecture aligned with the administrator's technical proficiency and desired level of control. The open-source community offers refined solutions that simplify the otherwise daunting complexity of building a mail server stack from component services (Postfix, Dovecot, etc.).
Mail-in-a-Box (MiaB) provides a comprehensive "turn-key solution" that automates the deployment and maintenance of a full-featured mail server and supporting services, including Nextcloud for file and groupware synchronization. This approach is ideal for rapid deployment and for organizations prioritizing low administrative overhead.
Sovereign adopts a more modular approach, utilizing Ansible playbooks to provision and maintain an entire "private cloud" infrastructure. This system manages a broad array of decentralized services beyond just email—including VPN, XMPP instant messaging, RSS readers, and extensive security monitoring. Sovereign is designed for administrators demanding granular control over every component, enabling configuration reproducibility and stability through Infrastructure as Code (IaC) principles.
Nextcloud serves as the indispensable companion layer, extending digital autonomy beyond email into file synchronization and collaboration. Its self-hosted nature ensures that files, contacts, and calendars are centralized and accessible under the direct control of the system administrator.
Deployment Phase I: Establishing the Mail Foundation
Establishing a self-hosted mail server requires meticulous preparation of the domain name and server environment, navigating specific constraints imposed by the global network infrastructure.
Prerequisites and Initial Server Preparation
A successful deployment requires a dedicated domain name, preferably one with a common Top-Level Domain (TLD) known to work well with mail services (e.g.,.com,.net,.info,.io). The server itself should run a clean, supported operating system instance (typically Ubuntu, as recommended by MiaB).
A critical initial hurdle involves the selection of a cloud or hosting provider. Many major providers, by default, block outgoing SMTP traffic on port 25 as an anti-spam measure. This necessitates proactive communication with the provider to request the opening of port 25, or the configuration of a third-party relay service. Relying on a third-party relay service, however, diminishes the ideal of pure self-hosting. The dependence on external cooperation concerning network traffic underscores that achieving digital autonomy is a continuous negotiation with the necessary interdependencies of the global email ecosystem, rather than an absolute escape.
The process begins with basic system maintenance and setup execution:
Bash
# Prepare the server environment
sudo apt update && sudo apt upgrade -y
sudo apt autoremove && sudo apt autoclean
# Execute the Mail-in-a-Box installation script (turn-key setup)
curl -s https://mailinabox.email/setup.sh | sudo -E bash
# Example execution for Sovereign (IaC setup):
# git clone https://github.com/sovereign/sovereign.git
# cd sovereign
# ansible-playbook -i./hosts --ask-sudo-pass site.yml DNS Configuration Strategy and Deliverability Risk
Mail deliverability is intrinsically linked to correct DNS configuration. The system's ability to successfully send email without being flagged as spam depends entirely on recipient servers trusting the domain’s authentication records.
MiaB’s default setup simplifies this process by requiring the administrator to delegate the domain's Name Server (NS) records to the Mail-in-a-Box server, allowing the box to automatically manage A, MX, and TXT records. Alternatively, if the root domain hosts a separate website (e.g., on a different IP address) or if the administrator prefers a different DNS host, the "External DNS" option must be used. In this scenario, the MiaB control panel provides a list of all required records which must be manually copied and maintained within the external registrar’s interface. When using external DNS, the administrator should only update the email-related records (MX, SPF, DKIM, DMARC), ignoring any suggestions to change A or WWW records pointing to the website.
A critical configuration for mail hygiene is the Reverse DNS (rDNS) or PTR record. This record ensures that the mail server's IP address (e.g., 192.168.88.8) resolves back to its official hostname (e.g., mail.example.com). Since the rDNS setting is controlled by the hosting provider or ISP, this requirement further demonstrates how achieving reliable mail service is dependent on external party cooperation.
Securing Mail Flow: Advanced DNS Authentication and Anti-Spoofing
Modern email security mandates the implementation of robust DNS-based authentication protocols (SPF, DKIM, and DMARC) to combat spoofing and enhance domain reputation.
Sender Policy Framework (SPF)
The SPF record, published as a DNS TXT record, explicitly lists all IP addresses or hostnames authorized to send email from the domain. When a receiving mail server performs an SPF check, it validates the sender's IP against this list.
The enforcement mechanism is critical. While a soft fail (~all) allows suspicious mail delivery , a hard fail (-all) is the stringent policy recommended for self-hosted mail, instructing recipient servers to reject messages originating from unauthorized sources. A domain may only possess one SPF record; if multiple services (e.g., the local server and a marketing platform) are authorized to send mail, their records must be combined using include: statements.
DomainKeys Identified Mail (DKIM)
DKIM introduces cryptographic validation to the email lifecycle. The self-hosted mail system generates a public/private key pair. The private key cryptographically signs outgoing messages, and the corresponding public key is published in DNS as a TXT record, typically under the mail._domainkey selector. This signature assures the recipient that the message originated from the domain owner and that the content was not altered in transit.
DMARC (Domain-based Message Authentication, Reporting, and Conformance)
DMARC serves as the policy layer, unifying the results of both SPF and DKIM checks and dictating the action recipient servers should take when authentication fails. It is published as a TXT record under the _dmarc subdomain.
The policy (p=) can be set to none (monitoring only) , quarantine (send failed messages to spam folders) , or reject (outright refuse delivery). The maximum security level for production domains is p=reject.
A mandatory component of DMARC implementation is the reporting function, configured via the rua=mailto: tag, which designates an email address (e.g., reports@example.com) to receive aggregate reports detailing authentication successes and failures. These reports are delivered as XML files. DMARC transforms authentication from a static defense measure into an active, continuous security monitoring process. By receiving and analyzing these reports, the administrator gains crucial threat intelligence, quickly identifying legitimate mail sources that are failing authentication due to misconfiguration (like an outdated SPF record) and, more significantly, detecting active malicious spoofing attempts targeting the domain.
The following table summarizes the essential DNS configuration for mail authentication:
Essential Email Authentication DNS Records
| Protocol | DNS Record Type | Host/Subdomain | Conceptual TXT Value | Policy Significance |
| SPF | TXT | @ (Root Domain) | v=spf1 mx a ip4:192.168.88.8 -all | Hard Fail policy restricts sending to server IPs specified in A/MX records. |
| DKIM | TXT | mail._domainkey | v=DKIM1; k=rsa; p=MIIB...[long key snippet] | Verifies message integrity via cryptographic signature. |
| DMARC | TXT | _dmarc | v=DMARC1; p=reject; pct=100; rua=mailto:reports@example.com | Enforces rejection of unauthenticated mail and provides failure visibility via RUA reports. |
Encrypted Transport Enforcement: MTA-STS and DANE/TLSA
Beyond merely authenticating the source, true transport integrity requires securing the connection against active attackers who may attempt to downgrade or strip the security protocols (Man-in-the-Middle attacks).
All people are equal! Except those wearing an umbrella.
MTA-STS (Mail Transfer Agent Strict Transport Security)
Standard email transfer relies on opportunistic TLS (STARTTLS). If the TLS handshake fails, the sending server often reverts to an unencrypted connection, making the transmission vulnerable to stripping attacks. MTA-STS mandates that external Mail Transfer Agents (MTAs) must connect securely using TLS 1.2 or higher, enforced by a valid certificate.
The MTA-STS policy is published via two mechanisms: a DNS TXT record and a plain-text policy file served securely over HTTPS from a specific A record (e.g., mta-sts.mail.example.com).
Postfix, the most common MTA in self-hosted deployments, supports MTA-STS through an smtp_tls_policy_maps plugin , which dictates the security level for outgoing connections. This configuration typically integrates with a local MTA-STS resolving daemon listening on a dedicated port :
Code snippet
# Postfix configuration in main.cf to enable policy lookups for MTA-STS
smtp_tls_policy_maps = socketmap:inet:127.0.0.1:8461:postfix
smtp_tls_CApath = /etc/ssl/certs/DANE (DNS-Based Authentication of Named Entities) and TLSA Records
DANE provides the highest level of transport security by eliminating reliance on the traditional Certificate Authority (CA) ecosystem, which is vulnerable to compromise and fraudulent issuance. DANE achieves this by utilizing DNSSEC to cryptographically bind the server’s TLS certificate (or its public key digest) directly to the domain name via a TLSA record.
DANE validation is conditional upon the integrity of the underlying DNSSEC chain. If the DNSSEC configuration for the domain is broken, DANE validation cannot be performed, and the system may revert to less secure CA checks or fail the connection outright. This confirms that advanced security mechanisms are interdependent; DANE offers maximum integrity but requires the stable foundation of DNSSEC. MTA-STS, conversely, offers robust, high-availability security for a wider range of endpoints while still relying on CA trust. Deploying both protocols leverages the strengths of each—MTA-STS for broad compatibility against downgrade attacks, and DANE for cryptographic integrity assurance against CA compromise.
The TLSA record must be placed at a specific DNS location: _[port]._[protocol].[domain] (e.g., _25._tcp.mail.example.com for SMTP). The value is a structured binary format represented in hexadecimal text, defined by three fields: Usage, Selector, and Matching Type :
A conceptual TLSA record structure example:
DNS Zone file
# Location: _25._tcp.mail.example.com [2]
# Type: TLSA
# Value: 3 1 1 370c66fd4a0673ce1b62e76b819835dabb20702e4497cb10affe46e8135381e7 [2]
# Usage (3): DANE-EE (match against the destination server's certificate) [8]
# Selector (1): Match public key [8]
# Matching Type (1): SHA-256 hash [8]Postfix versions 3.2 and later include features that simplify DANE implementation. DANE enforcement is activated within the Postfix master.cf configuration file by setting the specific security level for the transport :
Code snippet
# Postfix master.cf setting for DANE security enforcement
dane unix - - n - - smtp -o smtp_dns_support_level=dnssec -o smtp_tls_security_level=dane Modular Architecture: Postfix, Dovecot, and Rspamd Configuration
For those adopting a custom or Sovereign-like modular architecture , the integration of the MTA (Postfix), the Message Delivery Agent (Dovecot), and an advanced anti-spam filter (Rspamd) must be configured meticulously.

The Core Mail Stack Components
Postfix handles all outgoing SMTP traffic and routing, while Dovecot manages local mail delivery, storage (using IMAP/POP3 over SSL), and user authentication. In comprehensive systems, Dovecot and Postfix often utilize a centralized database (such as PostgreSQL or MySQL) to manage virtual users, domains, and aliases, decoupling user authentication from the operating system’s local user accounts.
Integrated Spam Filtering with Rspamd (Milter)
Rspamd is a high-performance, open-source spam filtering solution that utilizes machine learning, statistical analysis, and fuzzy hashes to score incoming messages. To maximize efficiency, Rspamd should intercept messages before Postfix fully accepts them, using the Milter protocol for pre-queue scanning. This approach conserves system resources and prevents known spam from touching local storage.
The integration requires configuring Rspamd to listen on a dedicated socket for the Milter protocol and instructing Postfix to utilize that socket.
Configuration steps involve:
- Installing Rspamd and Redis (for caching and classifier statistics).
- Configuring the Rspamd proxy worker to enable Milter mode and listen on localhost, typically port 11332.
The necessary Postfix configuration in main.cf integrates the Milter service:
Code snippet
# Postfix main.cf configuration for Milter
milter_protocol = 6
milter_default_action = accept
smtpd_milters = inet:127.0.0.1:11332 # Listening port for Rspamd proxy
non_smtpd_milters = $smtpd_milters
# Macros are needed for Rspamd to properly evaluate client data
milter_mail_macros = i {mail_addr} {client_addr} {client_name} {auth_authen} After integration, new inbound email should contain headers generated by Rspamd, such as X-Spam-Status:, confirming that scanning is active.
Historical Security Review: Data-at-Rest Encryption
The original push for enhanced mail server security, following events like the Snowden revelations, heavily emphasized encrypting data stored on disk , often recommending tools like EncFS or CryptKeeper. The "NSA-proof your e-mail in 2 hours" guide detailed setting up components like EncFS for on-disk encryption of the mail database.
While data-at-rest protection remains fundamental, the focus of architectural security has evolved. Early post-Snowden efforts centered on mitigating the risk of temporary server seizure or compromise by encrypting the storage endpoint. Modern expert deployments prioritize full-disk encryption (e.g., LUKS) managed at the OS/hypervisor layer, rather than application-level file system encryption like EncFS, which can be complex to maintain and may still expose metadata. The prevailing security strategy has shifted toward aggressively securing the transport integrity (MTA-STS, DANE) and authentication (DMARC) of the global delivery chain. This shift acknowledges that securing the global transmission path is often more impactful for mass privacy than implementing complex, potentially brittle local encryption schemas on an already hardened server.
Infrastructure as Code (IaC): Automating Maintenance with Ansible
The multifaceted complexity of a production-grade mail stack—encompassing components like Postfix, Dovecot, Rspamd, DNS records, and TLS certificates—makes manual management impractical and inherently error-prone. Infrastructure as Code (IaC) provides the necessary framework for resilience, reproducibility, and consistent security maintenance.
The Sovereign Methodology and Ansible Roles
The Sovereign project is built entirely on Ansible , an automation engine that provides idempotent configuration management. Idempotence guarantees that re-running the configuration scripts will reliably achieve the exact same desired system state, regardless of the server's starting condition. This capability is crucial for implementing auditable patches and ensuring rapid disaster recovery.
Ansible organizes configuration logic into reusable "roles," abstracting the complexity of file edits into manageable variable definitions. For example, Postfix and Dovecot roles manage certificate paths (dovecot_ssl_cert, postfix_ssl_key) and database connection details necessary for virtual user lookups .
Code Snippet: Integrating a Postfix Role via Ansible Playbook
A structured Ansible playbook, such as Sovereign’s site.yml , orchestrates the entire deployment by calling these specialized roles. The example below illustrates how a playbook defines the configuration variables required to set up the mail transport agent and integrate the Rspamd Milter service:
YAML
# Snippet from an Ansible site.yml playbook
- hosts: mail_servers
become: true
roles:
- role: MichaelRigart.postfix # Example of a modular Postfix role
vars:
postfix_inet_interfaces: all
postfix_main_config:
myhostname: mail.example.com
mynetworks: 127.0.0.0/8
smtpd_milters: inet:127.0.0.1:11332 # Explicit Rspamd Milter integration
- role: dovecot
vars:
dovecot_ssl_cert: /etc/ssl/certs/fullchain.pem
dovecot_ssl_key: /etc/ssl/private/key.pem Automation via IaC frameworks like Ansible is considered a mandatory operational requirement for expert-level deployments. Manual configuration inevitably leads to configuration drift, security lapses, and increased administrative overhead. IaC provides the consistency necessary to maintain robust security protocols like MTA-STS and DANE over the long term, ensuring the infrastructure remains auditable and patch-ready.
Nextcloud: Building the Private Collaboration Ecosystem
Nextcloud serves as the core file synchronization and collaboration platform, extending digital sovereignty to user data beyond the mailbox. Its adherence to open standards ensures broad client compatibility and seamless programmatic access.
Sleep right! Sleeping on your right side increases the efficiency of your sleep.
Synchronizing Groupware Data (CalDAV/CardDAV)
Nextcloud provides explicit support for standard open protocols to manage groupware data: CalDAV for calendars and CardDAV for contacts. This allows users to synchronize their private data across desktop applications (e.g., Thunderbird) and mobile devices (iOS, Android) without relying on proprietary vendor APIs .
Unlike centralized platforms that often obscure these access points, Nextcloud makes the connectivity endpoints clear, built upon the WebDAV standard :
Nextcloud Client Connectivity Endpoints
| Service | Protocol | Base URL Path | Client Use Case |
| Files / WebDAV | HTTPS | https://cloud.domain.com/remote.php/dav/files/USERNAME/ | File synchronization, bulk uploads, scripting access. |
| Calendar | CalDAV | https://cloud.domain.com/remote.php/dav/calendars/USERNAME/ | Synchronizing personal and group calendars. |
| Contacts | CardDAV | https://cloud.domain.com/remote.php/dav/addressbooks/USERNAME/ | Synchronizing address books and contact information. |
CLI File Management via WebDAV and cURL
For system administrators, WebDAV compliance allows direct, scripted interaction with the Nextcloud storage layer using standard HTTP tools like cURL. This capability is crucial for backend automation, staging data, or integrating files into custom workflows.
The use of cURL facilitates commands for creating directories or performing authenticated file uploads :
Bash
# Code Example: Creating a Directory with cURL (using MKCOL)
# Creates a new directory named with today's date using HTTP MKCOL method
curl -u user:pass -X MKCOL "https://example.com/nextcloud/remote.php/dav/files/USERNAME/$(date '+%d-%b-%Y')"
# Code Example: Uploading a File via WebDAV (authenticated)
# Uploads a local file 'report.pdf' to the user's Documents folder
curl -u 'user:password' --upload-file /tmp/report.pdf "https://cloud.example.com/remote.php/dav/files/USERNAME/Documents/report.pdf" Nextcloud's implementation of open standards means it functions as a highly flexible, self-owned API layer for data interaction. The administrator controls the server, the network policy, the storage medium, and the retention policies, ensuring the data ingestion and synchronization layer is fully programmatic and auditable. This moves data control away from reliance on vendor-specific proprietary APIs.
Data Resilience: Comprehensive Backup and Disaster Recovery Strategies
Digital sovereignty requires not only operational control but also data resilience. A complete backup strategy must adhere to best practices, such as the 3-2-1 rule (three copies, two different media types, one copy offsite), encompassing three core pillars: application configuration, database metadata, and user data.
The Three Pillars of Self-Hosted Backup
- Application/Configuration: Includes configuration files for the mail stack (Postfix, Dovecot) and Nextcloud, along with OS-level configurations.
- Database: Crucial for Nextcloud (file metadata, user configuration) and for mail servers utilizing virtual user tables (PostgreSQL/MySQL). The database must be quiesced or locked for a consistent dump .
- User Data: The actual mailbox files (typically Maildir format) and the entire Nextcloud user data directory.
Don’t skip breakfast. Studies show that eating a proper breakfast is one of the most positive things you can do if you are trying to lose weight. Breakfast skippers tend to gain weight.
Local Data Preservation with rsync
For efficient local, incremental backups, rsync is the industry standard for synchronizing large directories while preserving file attributes and permissions . Before backing up Nextcloud files, the application must be put into maintenance mode, and the database dumped to ensure file integrity and metadata consistency .
Bash
# Code Example: Nextcloud Data Directory rsync Backup
# Synchronizes the live Nextcloud directory to a local backup directory
rsync -Aavx nextcloud/ nextcloud-dirbkp_`date +"%Y%m%d"`/ Offsite Object Storage Backup (S3/S3-compatible)
While the objective is de-Googling, utilizing hardened, dedicated object storage services (such as Amazon S3 or compatible providers) for encrypted offsite backup is a standard requirement for physical redundancy. MiaB natively supports the automated backup of mailbox data to Amazon S3, simplifying the complexity of integrating offsite storage .
For modular or DIY solutions, the AWS Command Line Interface (CLI) provides the s3 sync command for mirroring local data to a remote bucket efficiently, only transferring files that are missing or changed based on size and last modified time .
Bash
# Code Example: AWS CLI s3 sync for Nextcloud/Mail Data
# Syncs local backup directory to a specific S3 bucket prefix, maintaining a mirrored state
aws s3 sync /srv/backup/nextcloud_data/ s3://my-private-bucket/mail-box-hostname/nextcloud/ --delete When implementing S3 backups, administrators must be aware of the economics of storage classes. Utilizing Infrequent Access (IA) tiers can save costs, but accessing objects stored in IA classes triggers specific access charges, potentially impacting the true cost if frequent restores or access attempts are necessary.
The establishment of true digital sovereignty necessitates incorporating an independent, robust offsite backup solution. Although utilizing a major cloud vendor for archival storage means trusting an external entity with encrypted copies of data, the operational risk associated with a single local drive failure far outweighs the security risk of storing highly encrypted backups with a provider specializing in high-availability, geographically redundant storage. The strategic decision shifts from ensuring complete control over the live service to ensuring control over the long-term archival, encrypted data.
Good night, sweetheart. Rest heals the body and has been shown to lessen the risk of heart trouble and psychological problems.
The movement toward digital autonomy
The movement toward digital autonomy through self-hosted mail and Nextcloud represents a fundamental shift in operational philosophy, prioritizing data control and resilience over the convenience of centralized platforms. Technical deployment requires meticulous attention across multiple layers, from foundational DNS hygiene (SPF, DKIM, DMARC) to advanced transport security (MTA-STS and DANE/TLSA).
The complexity of these integrated systems necessitates the adoption of Infrastructure as Code (IaC), exemplified by projects like Sovereign, which ensure the architecture remains auditable, reproducible, and consistently secured against configuration drift. Furthermore, extending autonomy through Nextcloud’s open protocols (WebDAV, CalDAV, CardDAV) provides a programmatic and self-owned layer for critical file and groupware management.
The final determination is that the initial investment in self-hosting—though technically demanding and subject to unavoidable ecosystem constraints (like ISP cooperation on rDNS and Port 25)—yields substantial long-term returns in operational risk mitigation and strategic control. The modern, expert-level self-hosted digital frontier is secured not by isolating the server, but by automating compliance with the highest standards of the global email ecosystem and ensuring redundancy through independent, encrypted backup strategies.

SPACELAUNCH NOW!
Get Your Site Up & Running
SpaceLaunch is an ideal choice for those seeking to swiftly establish their own website, it offers a comprehensive and user-friendly solution backed by essential features, FREE domain registration / transfer / renewal, 1h FREE technical support to get you going, and the flexibility to grow and expand as needed (add-ons available).